Uffelmann, E. et al. Genome-wide association studies. Nat. Rev. Methods Primers 1, 59 (2021).
Google Scholar
Fang, H. et al. A genetics-led approach defines the drug target landscape of 30 immune-related traits. Nat. Genet. 51, 1082–1091 (2019).
Google Scholar
Fujiki, D. et al. Genax: a genome sequencing accelerator. In 2018 ACM/IEEE 45th Annual International Symposium on Computer Architecture (ISCA) 69–82 (IEEE, 2018).
Zawistowski, M. et al. The Michigan genomics initiative: a biobank linking genotypes and electronic clinical records in Michigan medicine patients. Cell Genom. 3, 7 (2023).
Landry, L. G., Ali, N., Williams, D. R., Rehm, H. L. & Bonham, V. L. Lack of diversity in genomic databases is a barrier to translating precision medicine research into practice. Health Aff. 37, 780–785 (2018).
Google Scholar
de Vlaming, R. et al. Meta-GWAS accuracy and power (metagap) calculator shows that hiding heritability is partially due to imperfect genetic correlations across studies. PLoS Genet. 13, e1006495 (2017).
Google Scholar
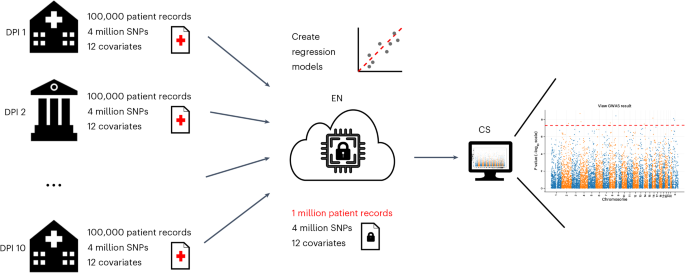
Froelicher, D. et al. Truly privacy-preserving federated analytics for precision medicine with multiparty homomorphic encryption. Nat. Commun. 12, 5910 (2021).
Google Scholar
De Cock, M. et al. High performance logistic regression for privacy-preserving genome analysis. BMC Med. Genom. 14, 1–18 (2021).
Blatt, M., Gusev, A., Polyakov, Y. & Goldwasser, S. Secure large-scale genome-wide association studies using homomorphic encryption. Proc. Natl Acad. Sci. USA 117, 11608–11613 (2020).
Google Scholar
Han, K., Hong, S., Cheon, J. H. & Park, D. Efficient logistic regression on large encrypted data. IACR Cryptol. ePrint Arch. 2018, 662 (2018).
Smajlović, H., Shajii, A., Berger, B., Cho, H. & Numanagić, I. Sequre: a high-performance framework for rapid development of secure bioinformatics pipelines. In 2022 IEEE International Parallel and Distributed Processing Symposium Workshops, 164–165 (IEEE, 2022).
Chen, H. et al. Logistic regression over encrypted data from fully homomorphic encryption. BMC Med. Genom. 11, 3–12 (2018).
Google Scholar
Chen, F. et al. PRINCESS: privacy-protecting rare disease international network collaboration via encryption through software guard extensions. Bioinformatics 33, 871–878 (2016).
Google Scholar
Aydin, F., Karabulut, E., Potluri, S., Alkim, E. & Aysu, A. Reveal: single-trace side-channel leakage of the seal homomorphic encryption library. In 2022 Design, Automation and Test in Europe Conference and Exhibition 1527–1532 (IEEE, 2022).
Resende, J. S., Sousa, P. R., Martins, R. & Antunes, L. Breaking MPC implementations through compression. Int. J. Inf. Secur. 18, 505–518 (2019).
Google Scholar
Li, Y., Xiao, D., Liu, Z., Pang, Q. & Wang, S. Metamorphic testing of secure multi-party computation (MPC) compilers. Proc. ACM Softw. Eng. 1, 1216–1237 (2024).
Google Scholar
Gentry, C. et al. Using fully homomorphic hybrid encryption to minimize non-interative zero-knowledge proofs. J. Cryptol. 28, 820–843 (2015).
Google Scholar
Kockan, C. et al. Sketching algorithms for genomic data analysis and querying in a secure enclave. Nat. Methods 17, 295–301 (2020).
Google Scholar
Hail-Team. Hail 0.2. GitHub (2023).
El-Hindi, M. et al. Benchmarking the second generation of intel SGX hardware. In Proc. 18th International Workshop on Data Management on New Hardware 1–8 (ACM, 2022).
Shringarpure, S. S. & Bustamante, C. D. Privacy risks from genomic data-sharing beacons. Am. J. Hum. Genet. 97, 631–646 (2015).
Google Scholar
Pinkas, B., Schneider, T. & Zohner, M. Scalable private set intersection based on OT extension. ACM Trans. Priv. Secur. 21, 1–35 (2018).
Google Scholar
Garimella, G., Pinkas, B., Rosulek, M., Trieu, N. & Yanai, A. Oblivious key-value stores and amplification for private set intersection. In Advances in Cryptology–CRYPTO 2021: 41st Annual International Cryptology Conference, CRYPTO 2021, Virtual Event Part II 41, 395–425 (Springer, 2021).
Dörre, F., Mechler, J. & Müller-Quade, J. Practically efficient private set intersection from trusted hardware with side-channels. In International Conference on the Theory and Application of Cryptology and Information Security 268–301 (Springer, 2023).
Pascoal, T., Decouchant, J., Boutet, A. & Esteves-Verissimo, P. Dyps: dynamic, private and secure GWAS. Proc. Priv. Enhancing Technol. 2021, 214–234 (2021).
Google Scholar
Zheng, W. et al. Opaque: an oblivious and encrypted distributed analytics platform. In Proc. 14th USENIX Conference on Networked Systems Design and Implementation 283–298 (USENIX Association, 2017).
Dokmai, N. et al. Privacy-preserving genotype imputation in a trusted execution environment. Cell Syst. 12, 983–993 (2021).
Google Scholar
Kocher, P. et al. Spectre attacks: exploiting speculative execution. In 2019 IEEE Symposium on Security and Privacy 1–19 (IEEE, 2019).
Mahlke, S., Hank, R., McCormick, J., August, D. & Hwu, W. A comparison of full and partial predicated execution support for ILP processors. In Proc. 22nd Annual International Symposium on Computer Architecture 138–149 (IEEE, 1995).
Lattner, C. & Adve, V. LLVM: a compilation framework for lifelong program analysis and transformation. In Proc. International Symposium on Code Generation and Optimization (CGO ’04) 75–88 (ACM, 2004).
Johnson, S., Makaram, R., Santoni, A. & Scarlata, V. Supporting Intel SGX on Multi-Socket Platform. Tech. Rep. Intel Corporation (2022).
Taassori, M., Shafiee, A. & Balasubramonian, R. Vault: reducing paging overheads in sgx with efficient integrity verification structures. In Proc. 23rd International Conference on Architectural Support for Programming Languages and Operating Systems, ASPLOS ’18, 665–678 (ACM, 2018); https://doi.org/10.1145/3173162.3177155
Dong, J., Rosenblum, J. & Narayanasamy, S. Toleo: scaling freshness to tera-scale memory using CXL and PIM. In Proc. 29th ACM International Conference on Architectural Support for Programming Languages and Operating Systems Vol. 4, 313–328 (ACM, 2024).
Dunn, T. et al. Squigglefilter: an accelerator for portable virus detection. In MICRO-54: 54th Annual IEEE/ACM International Symposium on Microarchitecture 535–549 (IEEE, 2021).
Fujiki, D. et al. Seedex: a genome sequencing accelerator for optimal alignments in subminimal space. In 2020 53rd Annual IEEE/ACM International Symposium on Microarchitecture 937–950 (IEEE, 2020).
Purcell, S. et al. Plink: a tool set for whole-genome association and population-based linkage analyses. Am. J. Hum. Genet. 81, 559–575 (2007).
Google Scholar
Schwarzschild, A., Goldblum, M., Gupta, A., Dickerson, J. P. & Goldstein, T. Just how toxic is data poisoning? A unified benchmark for backdoor and data poisoning attacks. In International Conference on Machine Learning 9389–9398 (PMLR, 2021).
Jang, Y., Lee, J., Lee, S. & Kim, T. SGX-bomb: locking down the processor via rowhammer attack. In Proc. 2nd Workshop on System Software for Trusted Execution 1–6 (ACM, 2017).
Simmons, S., Sahinalp, C. & Berger, B. Enabling privacy-preserving GWASs in heterogeneous human populations. Cell Syst. 3, 54–61 (2016).
Google Scholar
Uhlerop, C., Slavković, A. & Fienberg, S. E. Privacy-preserving data sharing for genome-wide association studies. J. Priv. Confid. 5, 137 (2013).
Fairley, S., Lowy-Gallego, E., Perry, E. & Flicek, P. The International Genome Sample Resource (IGSR) collection of open human genomic variation resources. Nucleic Acids Res. 48, D941–D947 (2019).
Google Scholar
Costan, V. & Devadas, S. Intel SGX explained. IACR Cryptol. ePrint Arch. 2016, 86 (2016).
Chen, G. & Zhang, Y. {MAGE}: mutual attestation for a group of enclaves without trusted third parties. In 31st USENIX Security Symposium (USENIX Security 22) 4095–4110 (USENIX, 2022).
Sambo, F., Di Camillo, B., Toffolo, G. & Cobelli, C. Compression and fast retrieval of SNP data. Bioinformatics 30, 3078–3085 (2014).
Google Scholar
Andrysco, M. et al. On subnormal floating point and abnormal timing. In 2015 IEEE Symposium on Security and Privacy 623–639 (IEEE, 2015).
Aldaya, A. C., Brumley, B. B., Hassan, S., Pereida García, C. & Tuveri, N. Port contention for fun and profit. In 2019 IEEE Symposium on Security and Privacy 870–887 (IEEE, 2019).
Bhattacharyya, A. et al. Smotherspectre: exploiting speculative execution through port contention. In Proc. 2019 ACM SIGSAC Conference on Computer and Communications Security 785–800 (ACM, 2019).
Ohrimenko, O. et al. Oblivious {Multi-Party} machine learning on trusted processors. In 25th USENIX Security Symposium (USENIX Security 16) 619–636 (USENIX Association, 2016).
Rosenblum, J., Dong, J. & Narayanasamy, S. SECRET-GWAS source code and data. Zenodo (2025).
link